Little Snitch Wired.meraki.com
- Little Snitch Wired.meraki.com Game
- Little Snitch Wired.meraki.com Movie
- Little Snitch Wired.meraki.com Song
Nov 02, 2017 Mac Use built in cam without indicator light? Thread starter ArtOfWarfare; Start date Mar 7, 2012; Sort (Likes) Forums. If the LED is wired directly to the camera sensor power connector in copper, then it's a bit hard to imagine the camera could still function in any way with no VCC. Little Snitch or the jailbroken iP Firewall tweak. Little Snitch. 1,273 likes 1 talking about this. Protect your privacy! Little Snitch informs you whenever a program attempts to establish an outgoing Internet connection and hence reliably prevents.
Oct 07, 2017 On the Mac I highly recommend to use Little Snitch and its profile functionality to achieve exactly that (I’ve wrote an article about Internet security while traveling before). On iOS devices, it’s unfortunately not that straightforward. Norbert wrote:Dear Little Snitch user community, With the release of Little Snitch 4.3 nightly (5237) we tried another approach to tackle the “delay during system startup on macOS Mojave” issue that some of you are experiencing. Jul 12, 2017 Not many casual users know about OS X’s Activity Monitor, and fewer still understand how it works and what it can really do. Here’s how to use Activity Monitor to manage your Mac’s memory, fix slow applications, and troubleshoot various other issues.
An application firewall is a form of firewall that controls input, output, and/or access from, to, or by an application or service. It operates by monitoring and potentially blocking the input, output, or system service calls that do not meet the configured policy of the firewall. The application firewall is typically built to control all network traffic on any OSI layer up to the application. Jun 19, 2018 WiFi Signal Strength Explorer is a handy little utility which unlike the normal WiFi icon, shows you the strength of connection via dots/percent in the menu bar and by clicking it, you can access some basic details about your current network. Wrapping Up: WiFi Analyser for Mac.
By now, any sentient IT person knows the perils of open Wi-Fi. Those free connections in cafes and hotels don't encrypt network traffic, so others on the network can read your traffic and possibly hijack your sessions. But one of the main solutions to this problem has a hole in it that isn't widely appreciated.
Large sites like Twitter and Google have adopted SSL broadly in order to protect users on such networks. But for broader protection, many people use a virtual private network (VPN). Most people, if they use a VPN at all, use a corporate one. But there are public services as well, such as F-Secure's Freedome and Privax's HideMyAss. Your device connects with the VPN service's servers and establishes an encrypted tunnel for all your Internet traffic from the device to their servers. The service then proxies all your traffic to and from its destination.
Auto-Tune Pro is the most complete and advanced edition of Auto Tune for Windows PC.It includes both Auto Mode, for real-time pitch correction and effects, and Graph Mode, for detailed pitch and time editing.For twenty years, the tool has been the professional standard for pitch correction, and the tool of choice for the most iconic vocal effect in popular music. AutoTune is a product developed by Analogx Sayit.This site is not directly affiliated with Analogx Sayit.All trademarks, registered trademarks, product names and company names or logos mentioned herein are the property of their respective owners. Download free auto tune for windows 10. Download the AutoTune installation file from the trusted download button link on above of this page Select Save or Save as to download the program. Most antivirus programs like BitDefender will scan the program for viruses during download. If you select Save, the program file is saved in your Downloads folder.
It's a better solution than relying on SSL from websites for a number of reasons: with a VPN, all of the traffic from your device is encrypted, whether the site you are visiting has SSL or not. Even if the Wi-Fi access point to which you are connected is malicious, it can't see the traffic. Any party that is in a position to monitor your traffic can't even see the addresses and URLs of the sites with which you are communicating, something they can do with SSL over open Wi-Fi.
But there is a hole in this protection, and it happens at connect time. The VPN cannot connect until you connect to the Internet, but the VPN connection is not instantaneous. In many, perhaps most public Wi-Fi sites, your Wi-Fi hardware may connect automatically to the network, but you must open a browser to a 'captive portal,' which comes from the local router, and attempt to gain access to the Internet beyond. You may have to manually accept a TOS (Terms of Service) agreement first.
Mar 24, 2017 Rekordbox beat grid sucks compared to Traktor Pro! Why is it that 95% of the tracks downloaded on Rekordbox box software is off. It takes me so much extra time to grid my beats after I buy tracks compared to Traktor Software. Mar 28, 2019 There have been substantial updates to Native Instruments’ Traktor Pro 3 DJ software in the past few months, and as Pioneer DJ’s Rekordbox DJ software continues to mature and grow in popularity, now seems like the perfect time to put these two DJ platforms head to head to see how they stack up against each other. Jan 16, 2019 There are four big platforms (Serato, Traktor, Rekordbox and Virtual DJ), and in this edition of our Head to Head series, we're comparing two of them - Serato DJ Pro and Pioneer DJ's Rekordbox DJ. Aug 12, 2018 DJ Tips - Serato DJ Pro vs Traktor Pro 3 - Duration: 10:27. PDotTV 19,643 views. Serato DJ Pro vs Rekordbox DJ - Which One Is Better? - Duration: 6:20. Digital DJ Tips 71,227 views. Traktor 3 dj software. A lot has changed in digital DJing since then, and today Serato’s latest app is called Serato DJ Pro (and Serato DJ Lite for beginners). It can be used with turntables, DJ media players and controllers. Traktor is Native Instruments’ laptop DJ software, and Traktor Pro 3 is the current version. It’s one of the first digital DJ apps, launching back in 2000.

In this period before your VPN takes over, what might be exposed depends on what software you run. Do you use a POP3 or IMAP e-mail client? If they check automatically, that traffic is out in the clear for all to see, including potentially the login credentials. Other programs, like instant messaging client, may try to log on.
I tested this scenario at a Starbucks with Google Wi-Fi while running Wireshark. Thousands of packets went back and forth on the open network before the VPN attempted to connect. A quick scan of the list found nothing that looked dangerous, and in fact the software on my system used TLS 1.2 in almost all cases, which was quite a relief. But your configuration may be different from mine, and even if your software attempts to use HTTPS, it could be vulnerable to attacks like SSLStrip, which tricks the software into using open HTTP anyway.
This gap in coverage may only be a matter of seconds, but that's enough to expose valuable information like logon credentials. Try running a network monitoring tool like Microsoft's TCPView for Windows or Little Snitch for Mac before you establish your Internet connection and see what happens in those first few seconds. The information may be protected by encryption, but it can carry details about your system configuration that could be used to identify it—or provide clues for an attacker.
Even beyond this time gap, sometimes VPN connections go down. At least in the default configurations of most operating systems, the applications on the system will fail over to the open Wi-Fi connection. Don't blame just the public VPN vendors. The same problem is true of corporate VPNs, unless they go to the trouble of configuring the system around the problem.
So, how do you do that? Shaun Murphy, a founder of PrivateGiant (www.privategiant.com), which makes products to protect the security and privacy of online communications, suggests that you do it with a software firewall, either one that comes with your operating system or a third-party one:
The basic approach is to prevent all inbound and outbound connections on your public networks (or zones) with the exception of a browser that you use to connect to captive portals and such. That browser should be one you only use for this purpose and, perhaps, some lightweight browsing (certainly not email, social, or any other personally identifiable purpose.) Using that same firewall, set up a profile/zone for VPN traffic where inbound / outbound traffic are less restricted (I recommend blocking outbound connections by default and then adding in programs as needed, it's surprising how many programs call home.. all the time.) The nice thing about this approach is your email client, primary web browser, and other applications you use will be useless unless you are actively connected to the VPN.
Sean Sullivan, security advisor at F-Secure, gave us the same advice with the useful addition that '..you'd want to launch the browser [for the captive portal] in 'safe mode' so the plugins are disabled.' If you're a Firefox or Google Chrome user, then Internet Explorer and Safari should fit the bill. You've got them on the system anyway.
Configuring firewall software on your PC to block non-VPN traffic isn't all that easy. It varies across operating systems and products, and it may not even be possible in Windows 8.1. On Windows, here's a summary of what you'd need to do:
- Connect to the VPN of your choice using the normal procedure for that product.
- In the Network and Sharing Center in Control Panel, make sure the VPN connection is set as a Public network, and the home or public Wi-Fi network is set as Home or Office (Home is better). (In Windows 8 and later this can be problematic unless the network connection is brand new, because Windows 8.x provides no user interface with which to change the location type—so the whole exercise may be impossible—unless you first delete and recreate all your network connections.)
- Finally, in the Windows Firewall in Control Panel go to the Advanced Settings. Create a rule to block all programs from connecting on Public networks. Then create a rule to allow both the VPN program and the browser you want to use for the captive portal to be allowed to connect on Public networks. You will need to set these rules both for inbound and outbound connections.
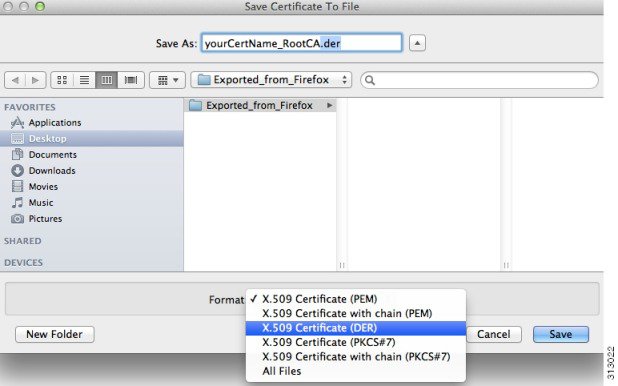
BolehVPN of Hong Kong has produced a more detailed set of instructions for using the Windows Firewall in Windows 7. On a Mac, you can achieve the same results with the aforementioned Little Snitch firewall. And Douglas Crawford at BestVPN.com has instructions for the Comodo Firewall on Windows, but says that he couldn't get the procedure to work on the standard Windows Firewall in Windows 8.1.
All in all, it's a fair amount of trouble to go through, and it's a configuration you'd only want on open Wi-Fi. If you work where there is secure WPA2 encryption on the Wi-Fi, then the VPN is probably not worth the overhead and the reduced network performance.
The real solution to this problem isn't hacking with firewalls, it's providing encryption by default in public Wi-Fi. This isn't done much now because that would mean supplying passwords, and the support overhead would just be too great for a cafe. The result is that we have an insecure situation with bad, but adequate, usability.
Little Snitch Wired.meraki.com Game
The Wi-Fi Alliance has had a solution for this problem nearly in place for years, called Passpoint. The Passpoint protocol was created to allow for Wi-Fi 'roaming' by creating a way for access points to grant access by way of a third-party credential, such as your Google ID or your ISP account. When you connect to a public access point through Passpoint, it authenticates you and establishes a secure connection using WPA2-Enterprise, the gold standard in Wi-Fi security—instead of leaving your traffic unencrypted or visible on the shared wireless LAN.
Little Snitch Wired.meraki.com Movie
The reason that you don't yet see Passpoint everywhere is that it requires the Wi-Fi provider—such as a consumer ISP, Google, or Boingo—to trust certain authentication providers and to advertise a list of them to connecting devices—the longer, the better. And users would need to configure Passpoint on their system to use one or more of their credentials when connecting to such a network. There hasn't been wide adoption of Passpoint yet—while it's been put to use in certain high-volume locations, such as many airports, it's still pretty uncommon.
Little Snitch Wired.meraki.com Song
The Wi-Fi Alliance now says that Passpoint is gaining traction in the enterprise as a way to handle BYOD. That's interesting if true, but it doesn't address the pain point of public Wi-Fi privacy. Passpoint has the potential to close the VPN data leakage window and make public Internet services far more secure. In its absence, there is no good solution.